Run AI agents safely in local sandboxes.
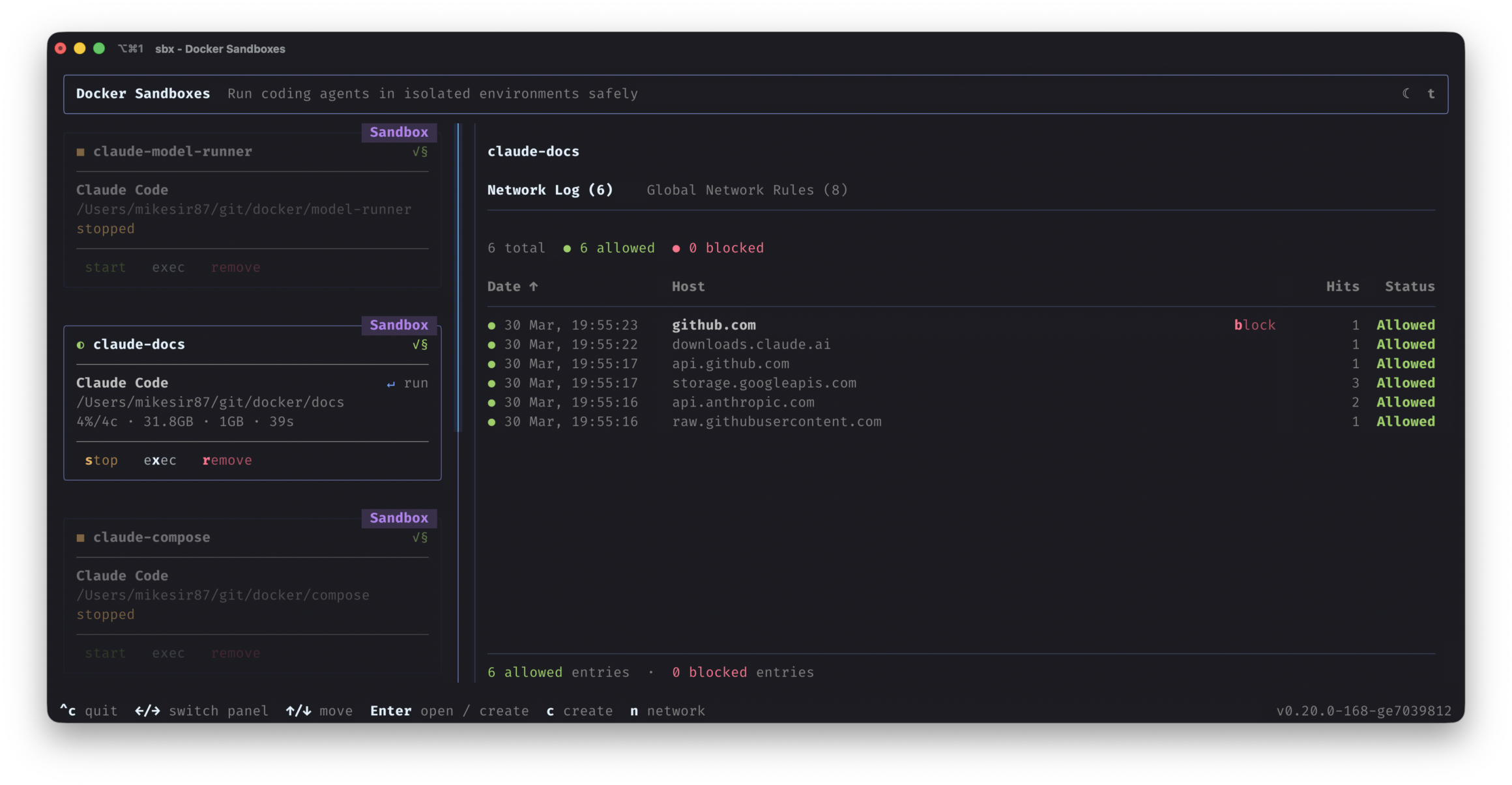
Sandboxes in action.

Get started in seconds.
Give agents the autonomy they need to get work done, safely.
Need to enforce these controls across your team?
Talk to an expertYOLO mode, safely.
Customizable Safe Execution
Network and filesystem controls you define.
MicroVM Isolation
Hard security boundary from the host.
Fast to Spin Up, Easy to Tear Down
Disposable by default. Faster than VMs.
Agents Can Use Docker Too
Agents can spin up containers within Sandboxes.
Real Dev Environment
Install packages, run services, work unattended.
One Sandbox for All Your Coding Agents
Claude Code, Gemini CLI, Copilot CLI, Codex, Kiro, OpenCode.
Works with leading coding agents
Common questions.
What is a sandbox for AI coding agents?
A sandbox is a microVM isolated environment that protects your filesystem and network from agents running inside it.
Which coding agents are supported?
Out of the box we support Claude Code, Gemini CLI, Copilot CLI, Codex, OpenCode, Kiro. You can also create your own
What does “YOLO mode” mean, and is it safe?
YOLO mode (--dangerously-skip-permissions) gives agents autonomy with no approval prompts. Essential for speed, but risky without guardrails. Sandboxes make it safe by isolating each agent inside a dedicated microVM.
How is a sandbox different from a VM?
Sandboxes run fully isolated in microVMs, giving more isolation without paying the full cost of running a VM. This lets them do things that need more permissions safely, like running additional Docker containers.
What safety controls can I configure?
Fine-grained control over networking, filesystem permissions, and resource limits — so agents get exactly the access they need and nothing more.
Do I need Docker Desktop to use sandboxes?
No.
What if I need additional admin controls?
Installing Sandboxes covers core functionality. For admin capabilities for a team (network restrictions and file system policies), talk to us to learn more.
Need More Control Over Your Sandboxes?
Talk to us about:
- Network access policies for sandbox environments
- Filesystem access controls and restrictions
- Admin-level configuration for your team